
Multiple zero-day vulnerabilities in digital video recorders (DVRs) for surveillance systems manufactured by Taiwan-based LILIN have been exploited by botnet operators to infect and co-opt vulnerable devices into a family of denial-of-service bots.
The findings come from Chinese security firm Qihoo 360's Netlab team, who say different attack groups have been using LILIN DVR zero-day vulnerabilities to spread Chalubo, FBot, and Moobot botnets at least since August 30, 2019.
Netlab researchers said they reached out to LILIN on January 19, 2020, although it wasn't until a month later the vendor released a firmware update (2.0b60_20200207) addressing the vulnerabilities.
The development comes as IoT devices are increasingly being used as an attack surface to launch DDoS attacks and as proxies to engage in various forms of cybercrime.
What Are the LILIN Zero-Days About?
The flaw in itself concerns a chain of vulnerabilities that make use of hard-coded login credentials (root/icatch99 and report/8Jg0SR8K50), potentially granting an attacker the ability to modify a DVR's configuration file and inject backdoor commands when the FTP or NTP server configurations are synchronized.
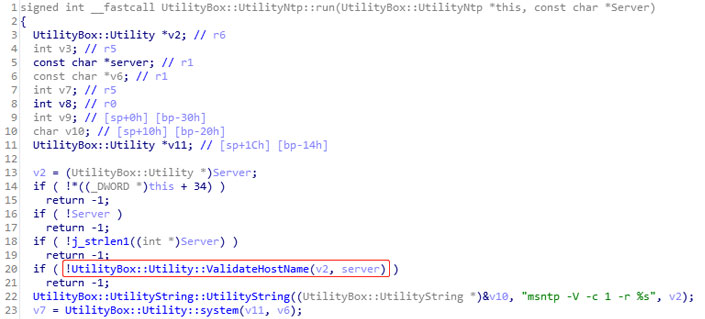
In a separate scenario, the researchers found that the process responsible for NTP time synchronization (NTPUpdate) doesn't check for special characters in the server passed as input, thus making it possible for attackers to inject and run system commands.
The newly patched version addresses the flaws by validating the hostname so as to prevent command execution.
Enforce Strong Passwords
Netlab said the operators behind Chalubo botnet were the first to exploit the NTPUpdate vulnerability to hijack LILIN DVRs last August. Subsequently, FBot botnet was found using the FTP / NTP flaws earlier this January. Two weeks later, Moobot began spreading through the LILIN 0-day FTP vulnerability.
The researchers said they reached out to LILIN twice, first after the FBot attacks, and then a second time after the Moobot infections happened.
Although Netlab didn't go into specifics of the motives behind the infections, it wouldn't be surprising if they were used by threat actors to perform distributed denial-of-service (DDoS) attacks on websites and DNS services.
"LILIN users should check and update their device firmware in a timely fashion, and strong login credentials for the device should be enforced," Netlab researchers said.
Comments
Post a Comment