
Cognizant Technology Solutions Corp, one of the largest IT services providers hit by Maze Ransomware Cyber Attack which causes service disruptions to its clients.
The company has more than 300,000 employees and it provides IT services, including digital, technology, consulting, and operations services.
Maze Ransomware Attack – Cognizant
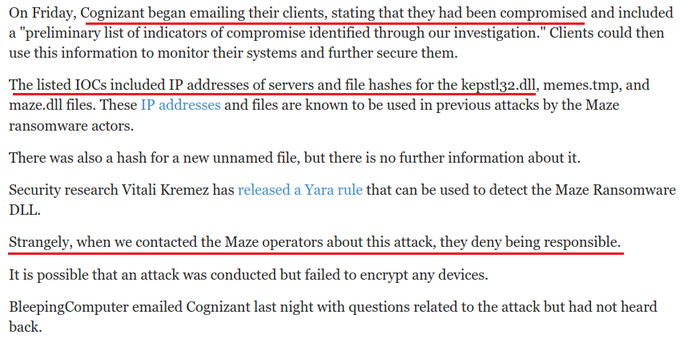
The company started emailing their client on Friday, stating that their internal systems hit by Maze ransomware attack.
“Cognizant can confirm that a security incident involving our internal systems, and causing service disruptions for some of our clients, is the result of a Maze ransomware attack,” reads the company statement.
The company said that they have implemented internal security associated with leading cyber defense firms and “taking steps to contain this incident”.
They also engaged with the law enforcement authorities, according to the statement posted to its website on Saturday.
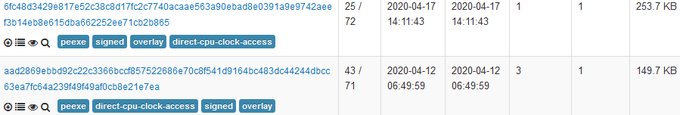
The company has informed their “clients and have provided them with Indicators of Compromise (IOCs) and other technical information of a defensive nature”.
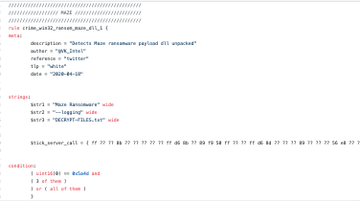
The maze ransomware was first observed in May 2019, operators behind the maze ransomware are known for stealing unencrypted files before encrypting them.
Then by using the stolen files, the operators will threaten the victims to pay the ransom or they will release the data.
Unlike other ransomware operators who use social engineering and spam email campaigns to attack targeted systems, the maze ransomware operators use exploit kits to place the foothold.
“If the Maze operators conducted this attack, they were likely present in Cognizant’s network for weeks, if not longer,” said Bleeping computer, who first reported the incident.
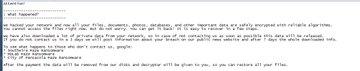
Once the encryption completed each file gets appended with different extension along with the original extension and the desktop wallpaper get’s changed to below.
Maze ransomware developed by skilled developers, they include a number of stealthy mechanisms and it poses a big threat to individuals and enterprises.
The ransomware attacks now become an easy and malicious way of robbing individuals and company’s can cost billions of dollars not to mention the privacy and safety implications.

 Pushed
Pushed 






Comments
Post a Comment